 World-leaders in Cryptography: Gene Tsudik
World-leaders in Cryptography: Gene Tsudik
ASecuritySite Podcast
Gene is a Distinguished and ICS Alumni Professor of Computer Science at the University of California, Irvine (UCI) where he has been since 2000. His research covers areas of security, privacy, and cryptography. From 1991 to 1996, he was a researcher at the IBM Zurich Research Laboratory and then at the Information Science Institute until 2000. He is a Fulbright scholar and a Fellow of the ACM, IEEE, AAAS, and IFIP. From 2009 to 2015, he was the editor-in-chief of the ACM Transactions on Privacy and Security (TOPS). Over the years, Gene has received a number of awards,...
info_outline World-leaders in Technology: Vint Cerf
World-leaders in Technology: Vint Cerf
ASecuritySite Podcast
Vint is seen as one of the founding fathers of the Internet, and along with Robert Kahn, was award the ACM AM Turing Prize - the Nobel Prize of Computer Science - in 2004. Vint contributed to many areas in the creation of the Internet, including writing many RFCs (Requests For Comment) drafts, and in 1974 published the classic paper of "A Protocol for Packet Network Intercommunication" in the IEEE Transactions on Communications. This paper basically defined the IP and TCP protocols that would eventually be used to build the Internet. Along with the A.M. Turing Award, he...
info_outline Panel Discussion: The Quantum clock countdown to Y2Q
Panel Discussion: The Quantum clock countdown to Y2Q
ASecuritySite Podcast
Panel Discussion: The Quantum clock countdown to Y2Q , CEO Scottish Centre of Excellence in Digital Trust and DLT , Founder and CEO ACubed.IT , Founder CyberSeQ J , Senior Researcher Cybernetica Estonia
info_outline Post Quantum Cryptography and Other Crypto with Daniel J Bernstein
Post Quantum Cryptography and Other Crypto with Daniel J Bernstein
ASecuritySite Podcast
A chat in the International Conference on PQC and AI. Daniel is a world-renowned computer scientist, one of the most influential figures in modern cryptography and a pioneer in post-quantum security.https://luma.com/9lxiupu6https://luma.com/9lxiupu6https://luma.com/9lxiupu6
info_outline Cryptography Experts: Professor Martin Albrecht
Cryptography Experts: Professor Martin Albrecht
ASecuritySite Podcast
Martin Albrecht is a Professor of Cryptography at King's College London and a Principal Research Scientist at SandboxAQ. He works broadly across the field of cryptography. His work focuses on the analysis of deployed or soon-to-be deployed cryptographic solutions and he has responsibly disclosed severe vulnerabilities to various public and private stakeholders such as OpenSSH, Amazon EC2, Apple, Telegram, Jitsi and Matrix. He further works on designing advanced cryptographic solutions. He is well known for analysing the security of lattice-based cryptography against classical and quantum...
info_outline World-leaders in Cryptography: Gilles Brassard
World-leaders in Cryptography: Gilles Brassard
ASecuritySite Podcast
Gilles has been a full Professor at the Université de Montréal for more than 45 years. He laid the foundations of quantum cryptography at a time when no one could have predicted that the quantum information revolution would usher in a multi-billion-dollar industry, much less that the United Nations would proclaim 2025 to be the International Year of Quantum Science and Technology. He is also among the inventors of quantum teleportation, which is one of the most fundamental pillars of the theory of quantum information. In addition to this, his research focuses on areas of classical...
info_outline World-leaders in Cryptography: Christof Paar
World-leaders in Cryptography: Christof Paar
ASecuritySite Podcast
Christof is a director at the Max Planck Institute for Security and Privacy in Bochum, Germany. He is also, a member of the German National Academy of Sciences Leopoldina and a Fellow of the IACR and IEEE. His research includes areas of light-weight cryptography, efficient cryptographic implementations, cryptographic Trojans and physical layer security. Christof is one of the co-creators of the PRESENT light-weight cipher and of the PRINCE block cipher, In 2003, he founded Escrypt GmbH together with Willi Mann-heims, and which was one of the first companies to focus on industrial...
info_outline Blockchain in Scotland
Blockchain in Scotland
ASecuritySite Podcast
info_outline World-leaders in Cryptography: Victor S Miller
World-leaders in Cryptography: Victor S Miller
ASecuritySite Podcast
Victor is a Senior Research Scientist at Nexus Laboratories. He received his PhD in Mathematics from Harvard University in 1975, and was an assistant professor at the University of Massachusetts Boston from 1973 to 1978. Victor has since worked for the IBM Research Center, The Institute for Defence Analyses in Princeton, Meta Platforms and SRI International. For his research, Victor has focused on areas of computational number theory, data compression and cryptography. Along with Neal Koblitz, he was the co-creator of Elliptic Curve Cryptography, the inventor of Miller's algorithm and...
info_outline Fireside Chat: Bruce Schneier
Fireside Chat: Bruce Schneier
ASecuritySite Podcast
A fireside chat from the International Conference on Digital Trust, AI and the Future. Bruce has created a wide range of cryptographic methods including Skein (hash function), Helix (stream cipher), Fortuna (random number generator), and Blowfish/Twofish/Threefish (block ciphers). Bruce has published 14 books, including best-sellers such as Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World. He has also published hundreds of articles, essays, and academic papers. Currently, Bruce is a fellow at the Berkman Center for Internet and Society at Harvard University.
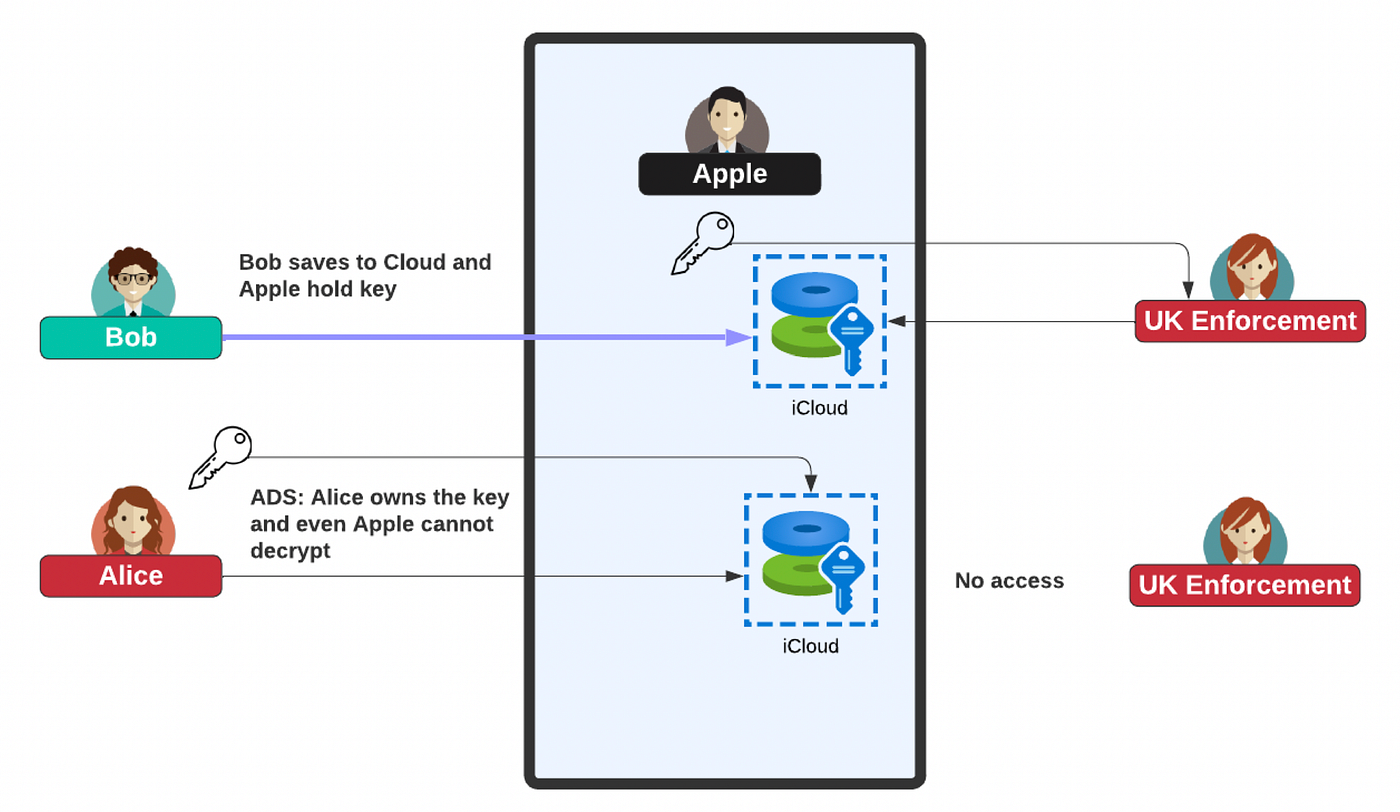
info_outlineThe fallback for law enforcement agencies has always been the place where files are stored, and all the best encryption within end-to-end communications will not stop unencrypted files at rest from being examined. But when the user encrypts data into the Cloud and where they hold their own keys, that’s when the nightmare begins for them.
The rise of cybersecurity on the Internet
Let’s pinpoint the start of cybersecurity on the Internet to the 1970s. This saw the rise of the Lucifer cipher and saw banks properly protect their communications. This led to the 56-bit DES encryption method, and which led many to suspect that the size of the key had been crippled due to the demands of law enforcement agencies. But, there was an even greater threat to these agencies evolving: public key encryption.
The rise of public key encryption started in the mid-1970s when Whitfield Diffie and Marty Hellman first defined a method that allowed us to secure our communications using a key exchange method — the Diffie-Hellman key exchange method. And then, almost a year later, Rivest, Shamir and Adleman presented a way to digitally sign a hash of data with the RSA signature method, and where a server could sign a hash of data with its private key and for this to be verified with an associated public key. For almost the first time, we could digitally verify that we were connecting to a valid system. But, the RSA method could not only sign data, it could also encrypt things with a public key, and where the private key could now be used to decrypt the data. It was a nightmare come true for law enforcement agencies.
What was magical about these methods was that you could encrypt data with keys that could be created for every single session — and generated and stored on user devices. User devices could even pick the keys that they wanted and their sizes and security levels. The days of security being crippled were fading fast. While the first versions of SSL were crippled by the demands for limits on this security, eventually, SSL evolved into something that could not be controlled. But, still files could still be viewed on user devices, so it was not a major problem for investigators.
Then, in 2001, the AES method was standardized by NIST, along with the newly defined SHA-256 hashing method, and we basically had all the security methods in place. But all of this did not please law enforcement agencies. For them, the rise of cryptography removed the opportunities that they had had in the past and where they could mass harvest information from phone calls or from the postal service. For the first time in history, citizens were free from spying from both those who protect nations and those who attack citizens. The Wild West years of the early Internet — and where little could be trusted — have subsided, and now we have systems which take encryption from one service on a device to another service on another device — end-to-end encryption.
End-to-end encryption
For some, end-to-end encryption was the final nail in the coffin for those who wish to monitor the tracks of citizens. This is data in motion, and where law enforcement agencies could still peak at data at rest and where the data is actually stored. Once data in motion and data at rest were encrypted, the door was effectively closed for peaking at data.
And, so, companies such as Apple advanced new methods which protected data at rest, and where all of a citizen's data could be encrypted onto the Cloud without Apple having the encryption key to view any part of it. For this, they created the Advanced Data Protection service:

This service protects things like citizens' photos, iCloud Drive, and wallet passes. For almost the first time, we had almost perfect security — and where five decades of advancement were finally coming together. We now have end-to-end encryption in apps such as What’s App and Signal, and Apple provides secure data storage.
But, some governments around the world saw the rise of privacy as a threat to their security agencies, and where the usage of encryption with file storage and over-the-air would mean that they could not monitor their citizens for threats against society. It is — and always will be — a lose-lose store on both sides. And, so, many governments have been calling for a back door in cryptography so that a “good guy” could get access to the citizen data and communication, but not a “bad guy”. Unfortunately, that’s not the way that encryption works, and where backdoors are a bad thing and difficult to hide.
So, the UK government has put pressure on Apple to provide them with a backdoor into their secure systems. For this, Apple would have to either provide them with a magic key to open up encrypted communications and file store, or dump their Advanced Data Protection system, and leave files unencrypted for investigation.
Apple stepping back
It would have been a difficult choice for Apple, but they have decided to drop their Advanced Data Protection system for UK users, and not go with the nightmare of a backdoor in their systems. Imagine if a terrorist had stored their files in iCloud, and law enforcement agencies had requested these files. Well, Apple would have to hold their hands up and say that they didn’t have the encryption files to access them, as the encryption keys were held by the user.
I trust Apple and believe they have some of the best security around. When was the last time you heard of someone getting some malware on an Apple system? They support a proper secure enclave and are advancing a privacy-aware cloud infrastructure for machine learning. They have also brought forward homomorphic encryption applications. Of all the big tech companies, Apple leads the way in terms of supporting the privacy and the security of users.
Conclusions
I feel sorry for Apple, as they have been painted into a corner. From a cybersecurity point-of-view, it is disappointing that Apple has been forced to step back on the Advanced Data Protection tool, as it was a great advancement in overcoming large-scale data breaches. And, like it or not, there is no magic wand that stops a bad actor from using something that a good actor has access to. Basically, if you leave your front door key under the mat, you have no guarantee that someone else will find the key and use it.
We have advanced cybersecurity for the past few decades and now use end-to-end encryption in a way we should have done from the start of the Internet. Of course, there are no winners in this, and society must find ways to protect itself from bad people, but opening up the whole of iCloud seems like a disaster waiting to happen.
The door is open for other more agile companies to support enhanced security and privacy, as the large tech companies seem to be applying the brake on some of their security advancements.
